In today’s fast-evolving digital landscape, the stakes for cybersecurity have never been higher. With the advent of AI technology, cyber threats have become more sophisticated and challenging to combat. Organizations, therefore, must adopt a proactive and multifaceted approach to protect their sensitive data and critical systems. In this article, we explore five crucial steps to strengthen your cybersecurity posture in an AI-driven world.
Being reactive and dealing with a cybersecurity breach is always more expensive than a proactive approach which compares your technology setup to best practices standards. Here are five things you can implement now to reduce your risk.
- Leverage the Power of the Cloud: In the age of AI, the cloud is a valuable ally in bolstering your cybersecurity defences. Cloud-based solutions offer scalable and adaptive security measures, allowing organizations to respond quickly to emerging threats. Implementing cloud-based security tools can provide real-time threat detection, rapid incident response, and centralized management of security policies. Leveraging the cloud ensures your cybersecurity infrastructure can adapt and evolve alongside the changing threat landscape.
- Organize a Robust Security Framework: An effective cybersecurity strategy begins with a well-structured security framework. Ensure that your organization has clearly defined security policies and procedures in place. Establishing a robust framework includes conducting regular risk assessments, defining access controls, and implementing a cybersecurity roadmap to improve based on cybersecurity best practices consistently. This proactive approach lays the foundation for a resilient cybersecurity posture that can withstand evolving threats.
- Deploy AI-Powered Defense Mechanisms: Organizations increasingly use AI-driven security solutions to protect them. Machine learning algorithms can analyze vast amounts of data to identify patterns and anomalies that may signify a cyber threat. AI can help automate threat detection and response, allowing security teams to stay ahead of cybercriminals. Integrating AI into your cybersecurity strategy gives you a proactive advantage in the ongoing battle against evolving threats.
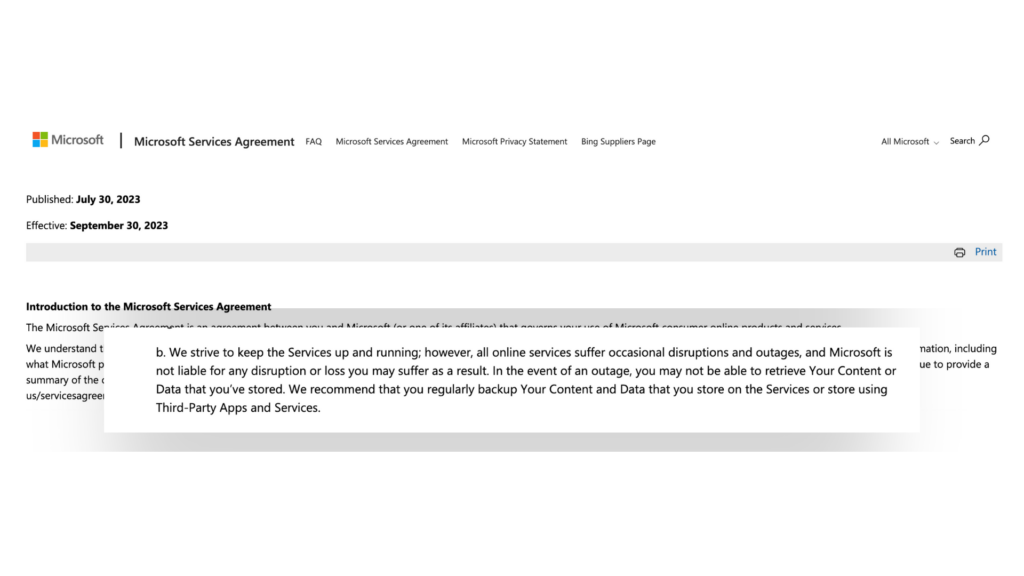
- Enhance Cloud-to-Cloud Backup with Third-Party Solutions: Most businesses think when they have their data in the cloud that means it’s effectively backed up. That is frequently not the case. Microsoft’s own services agreement (pictured above) recommends that businesses utilize a third party for backing up all their Microsoft 365 data to keep it safe. Make sure you have cloud-to-cloud backup for all your data. Third-party backup solutions offer a more comprehensive approach to data protection, providing file-level recovery options and additional layers of security. Moreover, many insurance companies now require organizations to have third-party backup solutions to qualify for cybersecurity insurance. Therefore, by incorporating third-party backup, you ensure a more robust and compliant data protection strategy that leaves no room for compromise.
- Train Your Team & Hold Them Accountable: Even the most advanced cybersecurity technologies are only as effective as the individuals using them. Implementing ongoing security awareness training is paramount. Cybercriminals frequently exploit human error, so educating your team about the latest threats and best practices is crucial. This training should be a collaborative effort but a continuous process to ensure that your staff remains vigilant against evolving cyber risks. Managers should review reports and hold their teams accountable for getting their training done. In an AI-driven world, where cyber threats are increasingly sophisticated, a proactive cybersecurity strategy is your best defence. By leveraging the cloud, establishing a robust framework, deploying AI-powered security measures, enhancing cloud-to-cloud backup, and prioritizing ongoing training and accountability, you can fortify your cybersecurity posture and protect your organization’s valuable assets from ever-evolving threats.
These five steps should serve as a starting point for enhancing your cybersecurity strategy. The most important thing is to take a proactive approach now to improve your cybersecurity and not wait until you have had an expensive breach.
Ready to Strengthen Your Cybersecurity?
Please don’t wait until it’s too late. Take the first step to protect your organization from cyber threats. Sign up for our FREE Cyber Risk Assessment today and gain valuable insights into your cybersecurity readiness.
Click here to sign up for our free Cyber Risk Assessment.